- Blog
- How Many Crypto Wallets Should I Have? (Complete Guide)

How Many Crypto Wallets Should I Have? (Complete Guide)
5 March 2026 • 17 Min ReadMost of the time, you need more than one wallet to safely manage your cryptocurrency. Different use cases need different setups, such as for long-term saving, daily transactions, and interacting with DeFi (decentralized finance) protocols.
This guide will talk about how many crypto wallets you might need, why having multiple wallets is good for security and privacy, and how to set up a wallet system that works for you.
What Is a Crypto Wallet?
A crypto wallet is a software program that lets people store, watch over, and use cryptocurrencies and other digital assets safely. A crypto wallet is different from other wallets because it doesn’t hold cash. Instead, it protects the cryptography keys that let you access blockchain-based funds. These wallets are necessary for anyone who works with cryptocurrencies because they let you store digital assets and execute transactions on different blockchains.
Wallets for cryptocurrencies are set up to handle both public and private keys. The public key is like an address for getting money, and the private key lets deals go through. Protecting the secret key is very important because having control over it means having control over the assets. If someone gets a hold of your secret key, you lose control of your funds forever.
Many current wallets offer extra features besides just making transactions easier, like connecting to decentralized apps, keeping track of your portfolio, and managing multiple assets. There are a lot of different levels of complexity in wallets, from simple mobile apps made for beginners to complicated hardware solutions made for people who need more security and control.
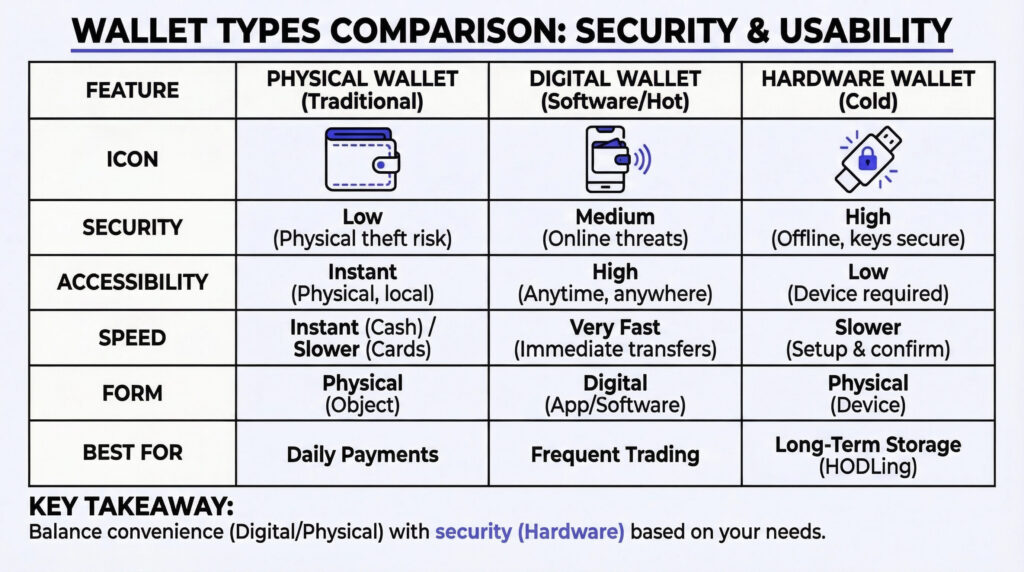
Different Kinds of Crypto Wallets Explained
Hot Wallets (Software Wallets)
The private keys for hot wallets are kept on machines that are connected to the internet and run software. These wallets let users quickly view, send, and receive cryptocurrencies. They come in the form of mobile apps, desktop programs, and browser extensions. Their main benefit is that they are convenient—you can get your money right away, and they’re usually easy to use.
Hot wallets can be used for everyday transactions and busy trading. But since they are always online, they are more likely to be hit by security threats like malware or illegal access. Users should use strong passwords and security tools like two-factor authentication to lower their risk.
Cold Wallets (Hardware, Paper Wallets)
Cold wallets are intended to keep private keys entirely offline, significantly reducing exposure to cyber threats. A hardware wallet is a special kind of physical device that keeps keys safe, away from computers and networks. They are highly recommended for storing cryptocurrency for a long time and for keeping larger amounts of it.
Paper wallets, on the other hand, are actual copies of a person’s keys. Paper wallets are cheap and can’t be hacked online, but they need to be kept safely and can get lost or ruined if kept unsafely. People who want to keep their money as safe as possible usually choose cold wallets.
Custodial vs Non-Custodial Wallets
This setup makes it easier to use wallets and get back into accounts, but it also puts all the trust in the provider. Non-custodial wallets, on the other hand, give all power and duty to the user, who is responsible for keeping their private keys safe on their own. Non-custodial wallets give you more privacy and freedom, but if you lose the keys to your wallet, you usually lose access to your money and can’t get it back.

Can You Have Multiple Crypto Wallets?
Having multiple bitcoin wallets is not only acceptable in real life, but also expected of anyone who takes digital assets seriously. If you have more than a few small crypto deals, you need to divide your holdings into different groups.
Why? Real-life experience demonstrates that consolidating all your assets into a single wallet exposes you to unnecessary risks. Without a structural split between holdings, a single lost private key, an attack by malware, or even a mistake made by a person can have effects that can’t be undone.
Investors and big players in the market never depend on just one wallet structure. Instead, they use layered wallet strategies, which include cold storage for their main reserves, separate “hot wallets” for operations, dedicated wallets for trying new protocols, and separate addresses for reporting compliance. This method isn’t about making things easier; it’s about being strong and in charge. The design of each wallet is based on threat models, audit requirements, and improving workflow. Each wallet plays a unique part in the overall security architecture.
Is It Legal to Have Multiple Crypto Wallets?
There are almost never limits based on law. Since a wallet is just a pair of cryptographic keys, nobody limits the number of wallets. When it comes to filing, stopping money laundering, and taxes, regulations do come into play, requiring individuals and organizations to adhere to specific reporting standards and practices to ensure compliance with financial laws. How well they record and keep track of their work is what separates professionals from amateurs.
Institutional custodians and funds, for instance, will keep records of every wallet, keep track of all asset flows, and keep logs for internal checks and regulatory reviews. When you don’t do this, even when you’re doing something acceptable, it often leads to problems or scrutiny.
The lesson is the same for private people with bigger holdings: the risk is not having too many wallets but mismanaging them—losing track, forgetting to record transactions, or failing to plan for backups and heirs.
How Many Crypto Wallets Can a Person Have?
The answer varies depending on the level of risk you are willing to take, the complexity of your operations, and the frequency of reporting required.
As a general rule, professionals will have at least three wallets: one for long-term storage (air-gapped, hardware-protected, and multisig if possible), one for everyday tasks, and one or more for new projects or activities with a lot of risk.
If you have ten or more wallets, you need a reliable way to name, track, and check them. The number is less important than your ability to stay aware and in control.

Why Would You Need Multiple Crypto Wallets?
How Multiple Wallets Protect Your Security and Privacy
Using more than one cryptocurrency wallet can make your security and privacy much better. Users can lessen the effects of a single point of failure by putting assets in different wallets. There is limited risk to the assets in one wallet if it is stolen. The funds in other wallets will not be affected. This method also lets you keep your valuable assets in a safer place, like a hardware wallet that is kept offline, while using different wallets for everyday activities. Managing money through separate wallets also makes it harder for outsiders to see all of a person’s wealth and activity. Such an arrangement can be a good privacy measure for people who are worried about their digital footprint or being watched.
Spreading your money out among different wallets lowers your risk
Having more than one crypto wallet can help you diversify your holdings and control your risk. Users can keep funds separate for different platforms, goals, or risk profiles by putting assets in different wallets. For instance, long-term holdings can be kept in a very safe wallet that doesn’t get much exposure to the public, while more active or experimental transactions are done in a different wallet. This split makes it less likely that the whole account will be lost if there is a technical glitch, security breach, or other unplanned event that affects a single wallet or platform. It also lets users spread their risk across different blockchain networks and wallet providers, making them even less reliant on a single solution.
Keeping Your Crypto Organized With Purpose-Built Wallets
Managing digital assets across multiple wallets makes things more organized and makes it easier to keep track of money. Users can more accurately track the movement of assets by setting aside different wallets for different activities, like daily buying, long-term savings, or taking part in decentralized finance. This separation makes it easier to keep records, track performance, balance books, and prepare paperwork for tax or accounting purposes. Keeping track of your wallets in an organized way can also help you avoid making mistakes or losing your money, since each wallet has a specific job to do in the bigger picture.
How to Decide How Many Crypto Wallets You Need
The number of crypto wallets you need depends on your goals, risk tolerance, and involvement with digital assets. There isn’t a single right way to do it. The best way depends on the user’s habits, the complexity of their portfolio, and how much power they want. People who are new to cryptocurrency might want to start with a single wallet that is simple to use and keep track of. As their needs change, they can add more wallets.
A multi-wallet approach is often better for more experienced users, especially those who trade, use decentralized finance, or diversify their assets. Keeping different wallets for different types of funds helps you better control risk, keep track of things, and protect your privacy. A more complicated setup is likely to be needed by users who hold large amounts of money, deal with multiple blockchain networks, or need separate wallets for business and personal use.
To determine how many wallets you need, consider which tasks require separate management, how much risk you’re willing to take with each part of your portfolio, and how much effort you’re willing to put into keeping everything organized and safe. It’s important to do regular reviews because both users’ wants and the cryptocurrency world can change over time.
Typical Wallet Setups by User Type
The following table shows how common wallets are set up based on user experience, security needs, and everyday use. Even though each user has different needs, these setups are generally thought to be the best in the crypto environment.
| User Type | Main Wallet Type(s) | Purpose / Activity | Security Level | Notes |
| Beginner | Software Wallet | Basic storage, sending, receiving | Standard | Simple to use, easy recovery |
| Advanced User | Software + Hardware Wallets | Trading, DeFi, protocol interaction | Higher | Multiple wallets for different activities |
| Long-term Investor | Hardware Wallet (Cold Storage) | Long-term holding, occasional transfers | Maximum | Offline storage for the largest balances |
| DeFi & NFT Enthusiast | Multiple Software Wallets | Staking, NFT management, and liquidity providing | Variable | Separate wallets per protocol or collection |
Best Practices for Managing Multiple Crypto Wallets
How to Set Up Multiple Wallets Safely
When you set up multiple crypto wallets, you need to be very careful about security right from the start. Establish each wallet in a secure location, ideally on a device that receives regular updates and is free from malware. Users shouldn’t get wallet software from sources that aren’t official, and they should always make sure that the apps and browser extensions they download are real. Setting up hardware wallets or “air-gapped” devices for long-term storage can help protect you from online dangers. During setup, private keys or recovery phrases should be backed up immediately and stored in a way that only the owner can access.
Categorize and Label Your Wallets
As the number of wallets grows, it’s important to keep them all in order. Giving each wallet a clear goal, like selling, saving, participating in decentralized finance, or managing NFTs, helps you keep track of your digital assets and lowers the chance of getting confused. Labeling wallets in software interfaces and keeping a private log or list of wallet addresses and what they’re supposed to do makes both daily tasks and long-term recordkeeping easier. Putting things into categories that make sense also helps with keeping track of performance and security, since the way each wallet is used can be changed based on its risk and exposure level, such as by categorizing wallets for high-risk trading versus low-risk savings.
Backup and Secure Recovery Phrases
It is important to protect access to every crypto wallet by backing up recovery words and private keys. If your device breaks, you delete something by accident, or you lose your login information, you won’t lose your assets if you have a reliable backup. The recovery phrase for each wallet should be kept in a safe and reliable place, like a safe deposit box, a real safe, or a backup device. If you use digital backups, they need to be encrypted and kept away. Recovery phrases shouldn’t be stored in easily accessible digital formats, like cloud storage or plain text files on internet-connected devices, as they can be accessed by unauthorized users. Checking files often to ensure they are complete and usable further lowers the risk of losing irrecoverable assets.
Use Trusted Devices and Secure Networks
The devices and networks used to access each wallet directly influence its security. Wallet operations, such as generating addresses, signing transactions, or making backups, should be performed only on devices that are regularly updated and free from malicious software. Avoiding the use of public or unsecured Wi-Fi networks is crucial, as these environments increase the risk of interception or unauthorized access to sensitive data. When possible, dedicate specific devices to wallet management, limiting their exposure to unnecessary applications or web browsing. Establishing strong, unique passwords and enabling additional authentication methods further enhances device security and reduces potential vulnerabilities.
Monitor and Audit Wallets Regularly
Effective wallet management requires ongoing oversight, especially when assets span multiple addresses and platforms. Regularly reviewing wallet balances, transaction histories, and recent activity can help identify unauthorized access, mistakes, or discrepancies early. Periodic audits also ensure that all wallets remain active, accessible, and in use as intended, reducing the chance of forgetting or neglecting funds. In addition to checking balances, reviewing backup procedures, and updating security settings as needed, it helps maintain resilience against evolving threats. Staying vigilant with routine monitoring preserves both the integrity and the value of the crypto portfolio over time.
Recommended Tools and Apps for Wallet Management
Managing several crypto wallets efficiently often requires the use of specialized tools and applications designed to simplify oversight and reduce manual effort. Portfolio tracking apps can aggregate balances and transactions from multiple wallets, providing a consolidated view of holdings and performance.
Some platforms allow users to set up notifications for incoming or outgoing transactions, track asset values in real time, and generate reports for tax or accounting purposes. When selecting wallet management tools, it is important to prioritize solutions with a strong reputation for security, transparent privacy practices, and compatibility with the specific wallets and blockchains in use. Choosing well-maintained software helps users maintain both convenience and safety as their digital asset portfolio grows.
How to Keep Track of Multiple Crypto Wallets
Use Portfolio Trackers and Aggregators
Portfolio tracking tools and aggregators provide a streamlined way to monitor balances and activity across multiple wallets and blockchain networks. These platforms consolidate information from various wallets into a single interface, enabling users to view their total holdings, recent transactions, and asset allocation without logging in and out of separate applications. Many portfolio trackers support real-time updates and offer additional features, such as performance analytics and automated alerts. Choosing a reputable, security-focused tracking solution helps maintain an accurate overview of assets while minimizing manual effort.
Keep an Updated Wallet Inventory/Spreadsheet
Maintaining a detailed and regularly updated record of all wallet addresses, along with their designated purposes, is a critical aspect of effective asset management. This inventory can be kept as a securely stored digital spreadsheet or as a physical logbook. By documenting key information, such as wallet type, usage category, backup location, and date of last access, users reduce the risk of forgetting important details or misplacing funds. Consistent record-keeping also simplifies portfolio review, supports tax reporting, and provides a reliable reference in case of technical issues or device loss.
Set Reminders for Check-Ins
Establishing regular check-ins helps ensure that all wallets remain accessible, secure, and up-to-date. Setting periodic reminders to review balances, confirm backup accessibility, and verify that no unauthorized transactions have occurred can prevent small issues from becoming significant problems. These reviews also provide an opportunity to update passwords, enable new security features, and reassess the need for each wallet in the broader portfolio. A disciplined routine of scheduled check-ins supports long-term asset protection and ensures management practices remain aligned with evolving needs.
Managing Taxes with Multiple Crypto Wallets
Tracking Transactions for Tax Purposes
Accurate tax reporting for cryptocurrencies relies on maintaining detailed records of all transactions, including trades, transfers, income, and expenditures. Maintaining comprehensive records becomes even more crucial when distributing assets across multiple wallets.
Users should document every movement of funds, including deposits, withdrawals, swaps, and conversions, along with relevant details such as dates, amounts, counterparties, and any associated fees. This documentation supports both annual tax filings and future audits, clarifying the origin and destination of each asset. A disciplined approach to tracking not only ensures compliance but also reduces the risk of errors or omissions that could result in penalties.
Recommended Tax Tools and Services
To simplify tax management, various software solutions and professional services are available that can aggregate transaction data from multiple wallets and exchanges, streamlining the process. These tools automatically import transaction histories, calculate gains and losses, and generate tax reports in accordance with local regulations.
Choosing a reputable tax platform that supports the specific blockchains and wallet types in use can streamline the entire process and reduce manual workload. For complex portfolios or when navigating unclear regulatory environments, consulting a tax professional with experience in cryptocurrency is advisable to ensure both accuracy and legal compliance.
FAQ
What’s the Proper Way to Decommission or Retire a Crypto Wallet Securely?
Retiring a crypto wallet must be done carefully to prevent unauthorized access or data leakage. First, transfer all assets from the wallet to a new, secure destination and verify the transactions on the blockchain.
For hardware wallets, perform a full factory reset and inspect the device to ensure all information is wiped. Please ensure that any written recovery phrases or seed backups are thoroughly destroyed rather than discarded intact.
For software or browser-based wallets, uninstall the application and delete all related files and backups. If you manage crypto for tax or audit purposes, document the date, reason, and confirmation of deactivation for future reference.
Is it Safer to Use Separate Wallets for Ethereum, Bitcoin, and Layer 2 Networks?
Yes, separating wallets by network reduces the risk of user errors and improves overall security. Using a single multi-chain wallet may be convenient, but it’s more susceptible to mistakes like sending assets to the wrong chain, which can result in permanent loss of funds if the assets cannot be recovered.
Creating dedicated wallets for each network (e.g., Ethereum, Bitcoin, Arbitrum, Polygon) allows for better control, cleaner organization, and fewer technical issues. It’s also a good idea to separate wallets based on use cases, such as trading, staking, and long-term storage.
How can Families or Teams Securely Manage Shared Crypto Wallet Access?
Sharing private keys or seed phrases is never recommended. Instead, use multi-signature wallets that require approvals from multiple participants to authorize a transaction.
Solutions like Gnosis Safe offer role-based access controls, transaction approvals, and detailed activity logs. Establish written access policies, define who can propose or approve transactions, and regularly review these settings as roles change.
Regular testing of recovery procedures is also essential to ensure everyone understands their responsibilities in case of an emergency.
How Can I Confirm that a Crypto Wallet App or Hardware Device is Authentic and Safe to Use?
Only download wallet applications from verified sources, such as official websites or trusted app stores. If available, verify digital signatures or hash values to confirm file integrity.
When purchasing hardware wallets, buy directly from the manufacturer or an authorized distributor. Check for tamper-evident seals and update firmware immediately upon first use using official channels.
Avoid second-hand devices from third-party marketplaces, as these carry a higher risk of being pre-configured or compromised.
Are There Insurance Options for Crypto Stored in Self-Custody Wallets?
Yes, though options are limited and typically geared toward institutional users and high-net-worth individuals. Some insurers offer coverage for theft or loss of crypto stored in hardware wallets, but policies often require strict security protocols, documented procedures, and third-party audits.
For individual users, the best protection remains sound operational security—offline storage, regular backups, and controlled access.
What Should I Do Immediately if My Crypto Wallet Is Hacked or Compromised?
Act quickly if you suspect a wallet breach. Begin by transferring any remaining funds to a new, uncompromised wallet created on a secure device. Then:
- Review transaction history for unauthorized activity.
- Revoke access or approvals granted to external applications.
- Change all related passwords and review device security.
- Destroy any exposed seed phrases or private keys.
- Document the incident in detail, especially for compliance or legal purposes.
For business or high-value accounts, an incident response plan should already be in place and tested regularly.