- Wiki
- What Is a Web3 Wallet?

What Is a Web3 Wallet?
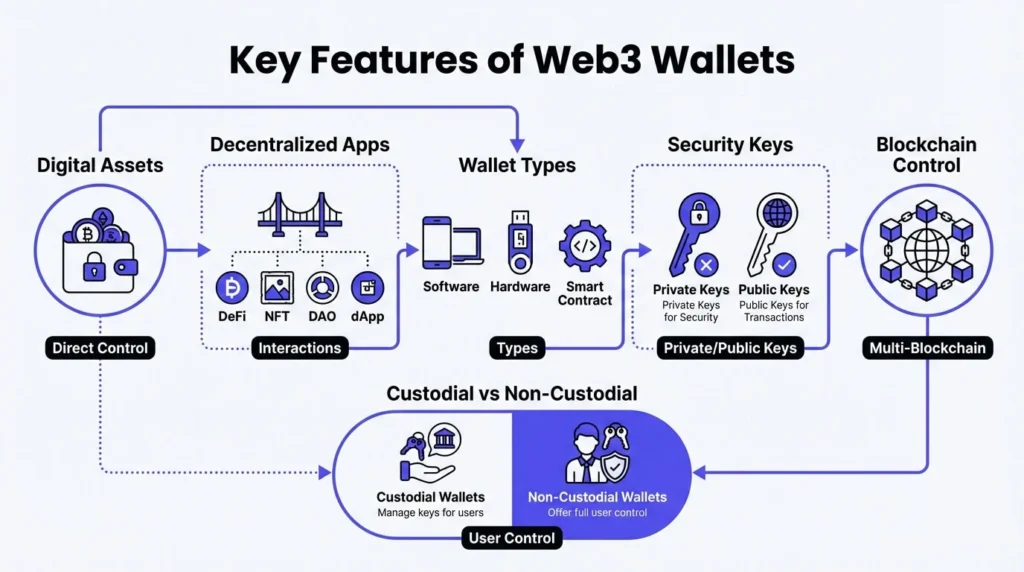
27 February 2026 • 26 Min ReadA Web3 wallet is an important part of the decentralized internet, which gives end users more control over their online experiences. Web3 wallets are different from traditional digital wallets linked to banks or login-based identity systems because they let people manage their digital assets, identities, and permissions directly on blockchain networks, without the need for third parties.
A Web3 wallet is more than just a place to keep cryptocurrency. It also acts as a cryptographic identity, a security layer, and a way to make transactions in decentralized ecosystems. It makes it easier to use decentralized finance (DeFi) apps, mint and send non-fungible tokens (NFTs), participate in decentralized autonomous organizations (DAOs), and use dApps without having to remember usernames, passwords, or go through a central authentication process.
There are different types of Web3 wallets, such as software, hardware, and smart contract-based ones. Each has its own pros and cons when it comes to security, usability, and flexibility. This article talks about the technologies behind them, how they work, the different types, the ways they can be used, and the risks that come with using them in blockchain-based environments.
How Does a Web3 Wallet Work?
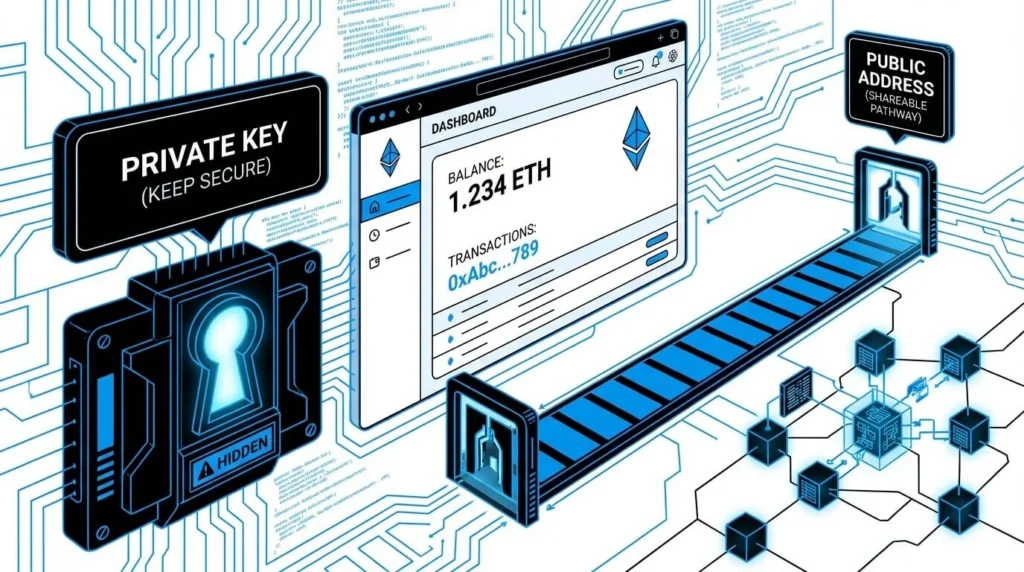
Private Keys and Public Addresses
A private key – which must be kept secret, and a public key – which can be shared, are the two keys that compose every Web3 wallet. Your public key (or a derived address from it) is like a username or account number on the blockchain. The private key, on the other hand, is the strongest proof that you own something. People use it to sign transactions to provide people access to money, tokens, or decentralized services.
If you lose your private key, no one, not even the wallet provider, can get it back. This model gives you accurate control and privacy, but it also makes you responsible: if you lose your key, you will never be able to get in again.
Web3 wallets are very different from Web2 accounts because they let you keep your own money. In Web2 accounts, authentication is done by centralized servers, and you can reset your password by email.
Interacting with Blockchain Networks
Web3 wallets are the gateway between the user and the blockchain. Your wallet creates a cryptographic signature using your private key when you do something, like send tokens, vote in a DAO, or mint an NFT. After that, the signed data is sent to the blockchain network, where nodes check it and record it as a transaction.
Every action is transparent and cannot be changed or undone once it has been confirmed. Web3 wallets let you interact directly with decentralized smart contracts and protocols on-chain, unlike traditional applications where you have to go through a company’s server.
Signing Transactions and Managing Digital Assets
Signing transactions is one of the main functions that a Web3 wallet does. When you “approve” something in a dApp, you’re really signing a request with your private key. This could mean sending tokens, granting a contract permission, or voting in governance.
Your wallet stores a copy of your account’s state (balances, assets, permissions) on your device, but the blockchain is the real source of truth. The wallet just shows this data and lets you interact with it in real time.
Additionally, wallets often support:
- Seeing how many tokens you have (fungible and non-fungible)
- Handling smart contracts’ approvals and allowances
- Connecting to more than one blockchain or layer 2 network
- Custom transaction settings like gas limits and fees
In short, a Web3 wallet is your control panel for the decentralized web. It is both a safe place to store your money and a way to make transactions, all linked together by cryptography.
Different kinds of Web3 wallets
There is no one type of Web3 wallet. The way they handle private key management, work with decentralized protocols, and deal with the trade-offs between security, usability, and autonomy all affect their design, logic, and operational models in big ways. There are different types of Web3 wallets, each based on a different idea about how people should use the decentralized internet.
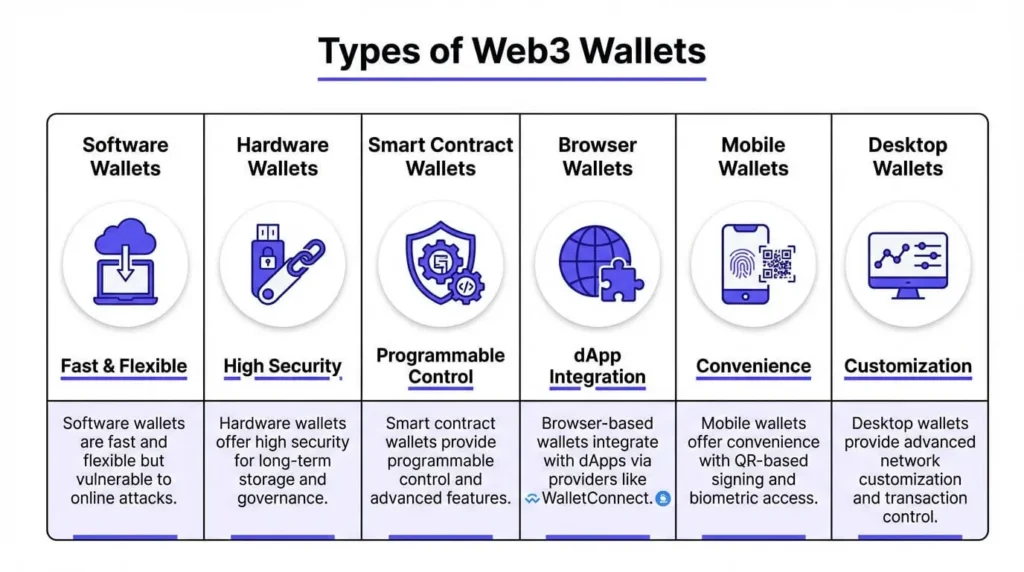
Software Wallets
Software wallets, also called “hot wallets,” are client-side programs that create and keep track of private keys on devices that are connected to the internet. In Web3, their main job is not just to store tokens, but also to authorize smart contract interactions, sign transactions, and control dynamic permission flows across dApps. Usually these wallets work as browser extensions (like MetaMask and Rabby) or mobile apps (like Trust Wallet and Rainbow).
They are gateways to the entire Web3 ecosystem, like decentralized finance platforms, NFT marketplaces, decentralized autonomous organizations (DAOs), and identity protocols. They are faster and more flexible because they run on active devices, but they are also more vulnerable to phishing, malware, and interface spoofing attacks.
Hardware Wallets
Hardware wallets are real devices that keep the user’s private key safe in a device that is not connected to the internet. In the world of Web3, they are important because they can sign sensitive transactions (like protocol governance and large-value transfers) without putting the private key at risk of being seen by any online system. These devices (like Ledger and Trezor) are very useful for people who own assets for a long time, DAO treasuries, and people who are in charge of governance.
Hardware wallets are not as easy to use for quick dApp interactions, but they are often used with software frontends to allow for safe cold signing of sophisticated contract calls. Keeping them separate from active internet sessions gives them a lot of protection in hostile environments.
Smart Contract Wallets
Smart contract wallets are on-chain wallets that can be programmed to use contract logic instead of static private keys to control who can access them and how they work. They support advanced features that regular wallets don’t, such as:
- Multi-signature authorization
- Daily transfer limits
- Role-based access control
- Social or guardian-based recovery mechanisms
Gnosis Safe, Argent, and Ambire are examples of this kind of platform. These wallets let DAOs, multisig collectives, and tech-savvy users build their own access frameworks right into the blockchain. They can also support gasless transactions through relayer networks and meta-transactions, which makes the user experience better without sacrificing decentralization.
Smart contract wallets are a more advanced layer of abstraction that fits well with Web3 logic: they are transparent, composable, and can be enforced by code.
Platform-Specific Web3 Wallet Interfaces
Web3 wallets can be differentiated not just by architecture, but also by interface and device context. The three primary interfaces are:
- Browser-based wallets, like MetaMask and Frame, are made to work well with dApps, mostly through injected providers or the WalletConnect protocol.
- Mobile wallets, like Rainbow and Trust Wallet, focus on portability and convenience by offering QR-based signing, push notification confirmations, and biometric access.
- Desktop wallets, like Exodus and Rabby desktop, let you customize your network more, access local data, and have more control over transaction metadata.
Different interface models meet different needs, from quick daily interactions to high-security operations. The choice often depends on how often and in what situations the wallet is used.
Custodial vs. Non-Custodial Control in Web3
The main difference in Web3 is not between wallets, but between who has the power to sign. A centralized service manages the private keys in custodial wallets, which is more like Web2 accounts and traditional exchanges. Users get easier recovery and onboarding, but they lose sovereignty, censorship resistance, and the ability to participate at the protocol level.
On the other hand, non-custodial wallets are very important to the Web3 philosophy. They give users complete control over key management, access authorization, and cryptographic signatures, which lets them take part directly in decentralized systems that don’t require trust. This model requires more responsibility (like keeping keys safe and knowing how to sign transactions), but it also makes the most of Web3.
In real life, a lot of advanced users use both types at the same time. They use custodial interfaces for fiat on-ramps and non-custodial wallets for protocol-level autonomy.
How to Set Up a Web3 Wallet
Setting up a Web3 wallet is a crucial initial phase if you want to use decentralized apps, keep track of your digital assets, and take part in blockchain-based ecosystems. The process is pretty simple, but you need to know a lot about key management and the implications of self-custody. Web3 wallets don’t let you recover your account through email or centralized support like traditional accounts do. The user is responsible for their own security.
Selecting the Right Wallet
A user should think about their priorities when choosing a wallet, such as how easy it is to use, how secure it is, what types of assets it supports, what networks it works with, and how comfortable they are with technology. For people who are new to Ethereum-based apps, browser wallets like MetaMask are a good choice because they are easy to use and have a lot of features. People who want to hold a lot of currency or use multiple chains may want to look into more advanced options like Rabby (multi-chain) or a hardware wallet for extra security.
Users should always check the source before installing anything because phishing clones of popular wallets are common. To avoid getting a hacked version of wallet software, you should only download it from trusted domains or repositories, like metamask.io or official GitHub pages.
Wallet Initialization and Seed Phrase Generation
The wallet will make a seed phrase, which is usually a string of 12 or 24 words based on a mnemonic standard (BIP-39), after it is installed. This phrase contains the private key that controls access to all linked addresses and assets.
Users are asked to write down the seed phrase offline, ideally on paper or a hardware device. You should never save it in digital form, like screenshots, cloud storage, or plain text files, because any device that is connected to the internet can be hacked.
You need to keep the seed phrase safe and private. Anyone who knows this phrase can move money around and control the wallet. There is no way to get it back if you lose it because decentralized systems don’t have a “reset” function.
Some advanced wallets let you make encrypted backups or use social recovery methods, but the seed phrase is still the only way to get your money back unless you set these up yourself.
Connecting to dApps and Signing Transactions
Once set up, the wallet can connect to decentralized apps through a standard interface, which is usually a “Connect Wallet” button on the dApp’s website. When the app connects, it can see the user’s public address and network status, but it can’t see their private keys or wallet contents.
When a user starts an action, like sending tokens or minting an NFT, the wallet asks them to review and approve the transaction. To approve, you have to use your private key to sign the request digitally. After that, the signed transaction is sent to the blockchain and the network processes it.
Users will also have to pay network fees (also called gas) at this point. These fees are paid in the blockchain’s native token, like ETH on Ethereum. Managing gas settings, transaction limits, and pending operations is an important skill for regular users, especially when the network is busy.
Setting up multiple wallets and networks
You can set up Web3 wallets to work with more than one account and network. For example, one installation of MetaMask can handle different wallets for personal, development, or business use. You can also add custom RPC details to make it work with other blockchains like Polygon, BNB Chain, or Avalanche.
Advanced users often keep their wallets separate based on how much risk they are willing to take. For example, they might use one wallet to try out new protocols and another (usually on hardware) to keep their long-term holdings. In decentralized settings, this kind of compartmentalization, which is often called “wallet hygiene,” is seen as a best practice.
Web3 Wallet Security Best Practices
Security is not an option in Web3; it is a necessary part of self-custody. Users in a decentralized environment have full control over the keys that let them access their digital assets. There are no middlemen, no ways for customers to get help, and no ways to get back into an account. Because of this, the wallet is both the key and the vault, and once that vault is broken into, it can’t be fixed.
The private key, or more specifically, its mnemonic representation, the seed phrase, is at the heart of this model. The seed phrase is not kept on a server like passwords are in centralized systems. It is made on the user’s device, stays there, and no one else can get it back. This design gives you the most control, but it also means that if you lose the seed phrase, you can’t get into the wallet or any of the assets in it.
Because of this, it is absolutely necessary to keep the seed phrase safe in order to use a non-custodial wallet. It should never be saved on a device that is connected to the internet. The most reliable way to store things is still to write them down by hand, make copies carefully, and keep them in different safe places. Some advanced users use encrypted hardware or cryptographic splitting techniques, but the basic idea is still the same: control must be complete and long-lasting.
Brute force and technical compromise aren’t the only things that can threaten the security of your wallet. Social engineering and interface-level manipulation are much more common. Phishing attacks that target Web3 users often look like wallet interfaces, recovery flows, or prompts to make a transaction. These tricks work not by breaking the protocol but by convincing users to give up their own security. To see and fight these vectors, you need to be technically savvy and have self-control.
Another risk that the public don’t think about enough is residual permissions, which are often left behind when people use smart contracts. If these token allowances aren’t kept in check, bad contracts could use them to take assets later. There are tools that let you check and take back these approvals, but not many people use them regularly. This makes an exposure surface that is not visible but is very real and lasts long after an interaction seems to have ended.
Web3 recovery planning is still a problem that hasn’t been solved. The seed phrase is the only thing that can go wrong with most wallets. Smart contract wallets are starting to change this by adding programmable recovery options, multisignature access control, and social guardianship models. But these solutions are still new and not all ecosystems support them equally. For now, high-assurance users have to make their own operational security plans that include both redundancy and privacy. They also need to plan for theft, forgetfulness, dislocation, and death.
To sum up, Web3 wallet security is not just about following best practices. It is about knowing that in decentralized systems, responsibility is not evenly distributed. Finality is absolute, reversibility is not possible, and safety is not a feature but a function of how the user designs the system.
The Trade-Offs of Web3 Wallets: Sovereignty vs. Convenience
Web3 wallets are different from other digital tools. They are not just ways to move assets; they are also ways to show the basic ideas of decentralization, individual sovereignty, permissionless access, and trustless interaction. But there are trade-offs to these features. Web3 wallets add features that traditional systems can’t have, but they also take away safety nets that users have come to expect. Finding the right balance between power and risk is very important.
One of the best things about Web3 wallets is that they switch from identity-based access to key-based authentication. Users don’t have to sign up, give out personal information, or use centralized platforms to prove ownership or use services. Instead, ownership is cryptographic and can be moved from one place to another. A private key, not a username or password, links assets, credentials, and transaction history. This makes it easy to move between platforms, lets people join open networks without permission, and creates a system where censorship or random account suspension is impossible.
Another important strength is interoperability. You don’t need separate accounts or integrations to use a single Web3 wallet with a lot of different apps, protocols, and financial systems. The wallet is always the same place to go to prove your identity and get permission, whether you’re trading on a decentralized exchange, voting in a DAO, or accessing token-gated content. When you add composable protocols to this, you get a user experience that is flexible and can be expanded without being limited by platform boundaries.
But these benefits come with some drawbacks that can’t be ignored. Self-custody, which is what makes non-custodial wallets unique, adds a lot of complexity. The user is completely responsible for keeping private keys safe, making backups, and spotting malicious interfaces. There are no password resets, no support tickets, and no legal guarantees. Mistakes are often permanent and, in some cases, very bad. This level of responsibility can be a turn-off for less tech-savvy users, not a selling point.
Also, usability is still a problem that won’t go away. Web3 wallet interfaces often show users ideas that are abstract, technical, or new to them. Most people who use Web2 systems have never had to deal with gas fees, transaction nonces, signing prompts, or blockchain confirmations. Some modern wallets try to make these complicated things easier, but this often means giving up some control and transparency.
Security holes make things even more complicated. The wallets themselves may be safe, but the dApps, interfaces, and contracts that make up the ecosystem around them add risks that the wallet can’t fully protect against. Even people who take basic safety measures are still falling for malicious approvals, fake tokens, front-end exploits, and social engineering schemes. Web3 systems are open by design, which means they are also naturally hostile.
Last but not least, regulatory uncertainty makes things even less clear. The legal status of assets in Web3 wallets is not clear in many places. Taxation, ownership rights, and consumer protections are not clearly defined, and people are still arguing about what wallet-based identity means. When wallets are used for governance, financial instruments, or pseudonymous commerce, users are in a legal gray area.
Web3 wallets are a sign of a bigger problem with decentralization: the trade-off between control and ease of use, finality and flexibility, and autonomy and complexity. The wallet is a powerful tool for managing assets and taking part in a completely new type of digital system for those who understand how it works and are okay with its limits.
Use Cases of Web3 Wallets
Web3 wallets do more than just give you access to funds; they also act as identity layers, permissioning interfaces, and programmable agents in decentralized networks. Their design lets users take part in a wide range of activities both on-chain and off-chain, without needing to coordinate with a central authority. This makes the Web3 wallet a credential that can be used in many different fields and is always changing.
Decentralized finance (DeFi) is one of the first and most important use cases. The wallet lets you interact with lending protocols, automated market makers, derivatives platforms, and decentralized exchanges without needing permission. Users can deposit assets as collateral, borrow stablecoins, provide liquidity, or take part in yield optimization, all without having to create accounts, send in documents, or use banking infrastructure. Smart contracts enforce the transaction logic, and the wallet’s signature is the only required authorization.
Another important area is NFT ownership and verification. You can use Web3 wallets to create, send, and check the ownership of non-fungible tokens (NFTs), which can stand for digital art, event tickets, intellectual property, or access credentials. You own an NFT if you have the wallet that it’s linked to. This makes it possible to have decentralized proofs of authorship, resale rights through embedded royalties, and application-level gating, where you can only access content or services if you own a token.
In governance systems, wallets are used as voting IDs. Decentralized Autonomous Organizations (DAOs) use token-based governance models. In these models, people with wallets can submit and vote on proposals that change the rules of the community, the direction of the protocol, or the allocation of funds. In many DAOs, the weight of a vote is based on how many tokens are in a wallet. This means that governance power is directly linked to on-chain identity. People usually vote by signing something or making an on-chain transaction, and the rules set by the smart contract decide the results.
Web3 wallets can also be used for on-chain identity and credentialing. Instead of using email addresses or usernames, decentralized identity models let users build verifiable credentials, like proof of participation, work history, or reputation, that are linked to their wallet address. These identities are portable and self-sovereign, so they can be used on different platforms without needing to be verified by a central authority. ENS (Ethereum Name Service), Lens Protocol, and Gitcoin Passport are all projects that look at different ways to use this identity layer by combining attestations with wallet-based authentication.
Web3 wallets are being used for more than just these well-known purposes. They are also being used for decentralized messaging, supply chain provenance, scientific publishing, and machine-to-machine communication. In each case, the wallet is treated as a programmable identity that can sign, verify, and approve actions. Cryptographic proofs make sure that the wallet can be verified.
These use cases are not separate from one another. A single user could be involved in many parts of the ecosystem at once, such as holding NFTs, using DeFi, voting in DAOs, and keeping their real name hidden. The Web3 wallet is the common base for all of these interactions. It connects different protocols to a single cryptographic agent.
As infrastructure continues to change and more real-world systems move toward on-chain primitives, the number of ways Web3 wallets can be used is likely to grow. This will not be by replacing traditional apps, but by providing a different trust model based on autonomy, composability, and verifiability.
How to Choose the Right Web3 Wallet
The different types of Web3 wallets show how different the ecosystem is. No one wallet can meet the needs of all users, and it shouldn’t either. Instead, wallets let you trade off on three main axes: control, complexity, and connectivity. To choose a wallet that fits the user’s operational context, risk model, and long-term goals, they need to understand these dimensions.
There is no one best wallet for everyone; there is only the best wallet for a specific purpose.
Control vs. Convenience: The Custody Trade-off
When choosing a wallet, the first thing to think about is whether you want custodial or non-custodial access. Custodial wallets, like those built into centralized exchanges, completely remove the need to manage keys. The user logs in with an email or device, and the service provider takes care of signing, recovering, and granting permissions in the background.
This model makes things a lot easier, but it also adds a central trust anchor. Users are at the mercy of the provider’s financial stability, rules, and safety measures. Non-custodial wallets, on the other hand, give the user full control and risk. The seed phrase is the only thing that can be trusted, and it gives you full control and no safety net.
The decision here is as much about philosophy as it is about practicality. Some users care more about custody and fail-safes, while others want censorship resistance and direct access. Both models have valid purposes.
Interface Depth: Matching Tools to Literacy
A hardware wallet offers military-grade security, but if a user can’t check an address before signing a transaction, its benefits are lost. On the other hand, browser-based wallets like MetaMask are easy to use, but they often show users raw hexadecimal data and contract prompts that are hard to understand without a technical background.
Wallets like Rainbow or Zerion that focus on clarity and abstraction can help beginners by making things easier to understand. Developers and users who are new to the protocol often need wallets that let them change the network settings, use multisig, and debug. Some users even employ wallet layering, using one for testing, another for storing valuable items, and a third for governance or DAO participation.
Don’t just assume that something is easy to use; make sure it fits the user’s current level of operational literacy.
Network Coverage: Not Every Wallet Speaks Every Chain
Many wallets started out as Ethereum-first tools, but the multi-chain era has made it necessary for wallet developers to add support for more protocols. Still, chain compatibility isn’t always the same. A wallet made for Solana might not work with EVM chains. Keplr is a Cosmos-native wallet that won’t work with decentralized applications (dApps) that are based on Ethereum. Some wallets work really well with certain ecosystems, while others try to work with all of them, but they often have to give up depth for breadth.
When you choose a wallet, you also choose an ecosystem. In some cases, it means having more than one wallet to fully take part in different areas.
Feature Scope: Identity, Permissions, Recovery
More and more, wallets do more than just manage keys. They also have identity frameworks, social features, and programmable logic. Smart contract wallets, for example, have features that traditional wallets don’t, like role-based access, delegated signing, and account recovery. Some have DAO interfaces, in-wallet swaps, or even messaging protocols built right in.
The important question is whether the wallet is just a key vault or a user agent.
These extra features are more than just nice to have if someone wants to use DAOs, identity services, or credential systems; they are necessary for the system to work.
Risk Profile: What You Stand to Lose
A wallet that is connected to DeFi protocols and holds a lot of money needs a different way of thinking about threats than one that is used to mint NFTs or testnets. Cold storage and multisignature controls are standard for situations with a lot of risk. For transactions that happen often but aren’t worth much, the trade-off may be in favor of browser or mobile wallets that put speed and ease of use first.
It’s not about being paranoid. It’s all about alignment. Choosing a wallet isn’t about branding or popularity; it’s about managing exposure.
No Single Wallet, and That’s by Design
Web3 does not say how to get in. Its design allows for modularity and even requires it. Users are encouraged to have multiple wallets for different situations. This reduces risk, makes the user experience easier, and keeps options open.
There is no lock-in, no forced unification, and no one point of failure; there are only tools that do their jobs. You could use a cold wallet that focuses on security with a test burner wallet. A governance wallet might not be used for anything other than protocol votes. You can set up identity wallets, organizational wallets, and grant participation wallets to do specific tasks, each with its own risk envelope.
It’s not about choosing the “right” wallet; it’s about topology.
FAQ about Web3 Wallet
Do I need a Web3 wallet if I just want to buy cryptocurrency?
Not always. A centralized exchange like Coinbase or Binance lets you buy and hold cryptocurrencies like Bitcoin or Ethereum without using a Web3 wallet. This is fine if you don’t want to use decentralized applications (dApps).
A Web3 wallet is necessary if you want full control over your assets, want to participate in DeFi protocols, want to collect NFTs, or want to be involved in DAO governance.
What is the best Web3 wallet for beginners?
There is no one “best” wallet, but some are easier for beginners to use. MetaMask is popular because it’s easy to set up as a browser extension and works with a lot of dApps. Trust Wallet and Rainbow have easy-to-use interfaces and quick onboarding for people who use their phones first.
To avoid phishing scams, always get wallets from trusted sources.
Is a Web3 wallet the same as a crypto wallet?
Not quite. People often use the terms interchangeably, but they mean different things. A “crypto wallet” is usually software or hardware that keeps and moves cryptocurrencies. Send, receive, and store are the main things its design is based on.
On the other hand, a “Web3 wallet” is more than just a place to store assets; it also serves as an authentication mechanism, an identity layer, and an interface for interaction within decentralized protocols. It lets people sign messages, give permission for dApps to access them, take part in governance, and even store reputational metadata.
Basically, all Web3 wallets are crypto wallets, but not all crypto wallets are Web3 wallets. The difference is whether the wallet supports decentralized, programmable interactions that go beyond simple transactions.
What happens if I lose my private key or seed phrase?
If you lose your seed phrase in a non-custodial Web3 wallet, you’re done. The wallet doesn’t keep your keys; it makes them on your device, and the seed phrase is the only way to get them back. If you lose it, you will never be able to access all of the addresses, assets, and credentials that are linked to it. There is no way to get help from customer service, reset your password, or get a recovery email.
Some smart contract wallets, like Argent or Safe, have recovery plans that use trusted guardians or multi-factor authentication, but these aren’t yet standard across the ecosystem. Users should treat their seed phrase as if it can’t be replaced, both legally and functionally.
Can I use one wallet for everything?
Yes, in theory; no, in practice. Most wallets can handle multiple types of transactions (DeFi, NFTs, DAOs, identity), but using the same wallet for everything makes it more vulnerable to attacks, exposes your privacy, and increases operational risk.
Best practice in Web3 involves wallet segmentation:
- One address for storing assets (cold storage),
- Another for high-frequency interaction (hot wallet),
- And optionally one for governance, testnets, or identity anchoring.
This separation makes it easier to model risks, follow audit trails, and reduce the number of ways that losses can happen. Think of it as operational compartmentalization, which is just as important in cybersecurity as it is in decentralized infrastructure.
Are hardware wallets still necessary in the age of smart wallets?
Smart contract wallets offer programmable security, social recovery, and flexible access control. However, they still rely on the blockchain being available, the contract being correct, and the supporting infrastructure.
On the other hand, hardware wallets work when you’re not connected to the internet. They never give internet-connected devices access to the private key, which makes them immune to most remote attack vectors. Cold wallets are still the best way to store high-value items.
Even so, the rise of smart wallets doesn’t mean the end of hardware wallets. Instead, it creates a new way of doing things that values flexibility over extreme isolation. There is a use case for each model; the most secure setups usually use both.
How private is a Web3 wallet?
A Web3 wallet doesn’t give you privacy; it gives you pseudonymity. Public blockchains keep track of all transactions. By default, your real name is not linked to your wallet address. However, your activity history, balances, token holdings, and contract interactions are all fully visible and traceable. It’s hard to break the link between an address and an identity once it exists, even if it’s not official.
Protocols like Tornado Cash tried to fix this by adding transaction obfuscation tools, but these tools are getting more and more attention from regulators. There are other models that privacy-preserving chains like Zcash and Aztec suggest, but they haven’t been widely used in dApp ecosystems yet.
Most people can’t really be private on Web3 unless they do things like separate their addresses, use mixing protocols, or zero-knowledge proofs.
Why do some users maintain multiple Web3 wallets?
One wallet is enough to access most decentralized applications, but many experienced users keep multiple wallets on purpose to manage risk, protect their privacy, and keep their intentions separate.
For instance:
- A cold wallet is used for long-term storage and is never connected to dApps.
- A hot wallet (often browser-based) is used for everyday interaction with smart contracts and platforms.
- A governance wallet may be used exclusively for DAO voting, with tokens delegated from another address.
- A burner wallet is used temporarily for minting NFTs or exploring new dApps in a sandboxed environment.
It’s not about convenience; it’s about keeping things clean. It limits exposure in case of a front-end exploit, lowers the risk of phishing, and lets you use different security models for different tasks. It also makes it harder to build a full behavioral profile of a user across different apps and chains.
In short, having more than one wallet isn’t a problem. They are a type of self-imposed segmentation that fits with the ideas of modularity and minimization. In a system without trust, those rules are often the best way to protect yourself.